Understanding Cybersecurity Policies Governance Terms
/ 3 min read
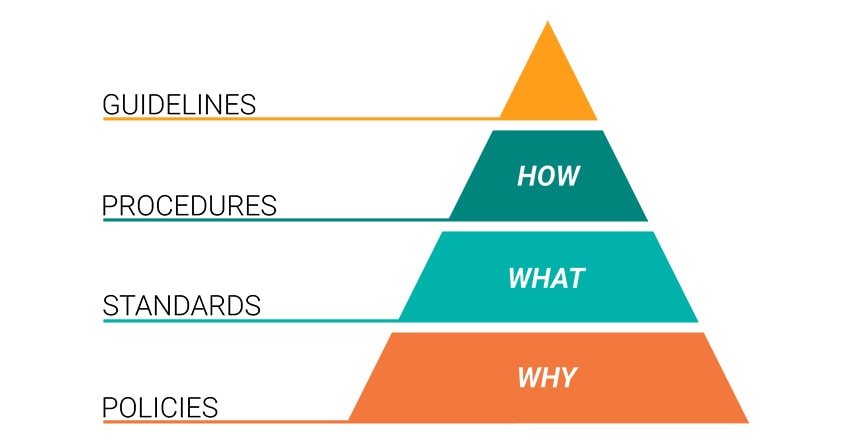
Policies, Standards, Procedures, and Guidelines
Cybersecurity governance follows a structured hierarchy, ensuring security is applied consistently across an organization. The four levels in this hierarchy are1:
- Policies (WHY) → Set the direction and purpose.
- Standards (WHAT) → Define mandatory requirements.
- Procedures (HOW) → Provide step-by-step implementation.
- Guidelines → Offer recommended best practices.
1. Policies – The WHY
A policy is a high-level statement that defines an organization’s security intent and objectives. It sets the rules that must be followed but does not explain specific technical details.
Example:
A Password Policy might state:
- “All employees must use strong passwords and change them every 90 days.”
Policies provide the “WHY” behind security controls but do not dictate how to enforce them.
2. Standards – The WHAT
A standard defines the mandatory technical security requirements to enforce policies consistently across an organization.
Example:
A Password Standard might include:
- Passwords must be at least 12 characters long.
- Passwords must contain uppercase, lowercase, numbers, and symbols.
- Account lockout after 5 failed attempts.
Standards answer the “WHAT” needs to be done to comply with policies.
3. Procedures – The HOW
A procedure is a step-by-step document explaining how to implement a policy or standard in practice.
Example:
A Password Reset Procedure may include:
- Go to the password reset portal.
- Enter your current password.
- Create a new password that meets the Password Standard.
- Confirm and save the new password.
Procedures answer “HOW” security rules are applied.
4. Guidelines – Best Practices
A guideline provides recommended (but not mandatory) best practices for security.
Example:
A Remote Work Security Guideline may suggest:
- “Use a VPN when accessing company data from public Wi-Fi.”
- “Enable multi-factor authentication (MFA) on all accounts.”
Guidelines are optional but help improve security when followed.
Summary Table
| Term | Purpose | Example |
|---|---|---|
| Policy | Defines security rules (WHY) | “Employees must use strong passwords and change them every 90 days.” |
| Standard | Defines mandatory security (WHAT) | “Passwords must be at least 12 characters long.” |
| Procedure | Step-by-step instructions (HOW) | “Go to the password portal, enter old password, create a new strong password, confirm and submit.” |
| Guideline | Best practices (optional) | “Use a VPN when accessing company data from public Wi-Fi.” |
CISSP Exam Tips
If you are preparing for the CISSP (Certified Information Systems Security Professional) exam, understanding these terms is essential. Here are some key exam tips:
- Policies = High-level rules and company expectations (e.g., “We must have strong passwords”).
- Standards = Mandatory requirements (e.g., “Minimum password length: 12 characters”).
- Procedures = Step-by-step implementation (e.g., “Go to settings → Change password”).
- Guidelines = Suggested best practices (e.g., “Use a VPN when working remotely”).
CISSP Exam Tip:
You may see scenario-based questions asking which document (Policy, Standard, Procedure, or Guideline) applies in a given situation.
For example:
An organization requires encryption for all email communications. What type of security document is this?
Answer: Standard
Final Thoughts
By understanding the difference between Policies, Standards, Procedures, and Guidelines, organizations can improve their cybersecurity posture and reduce security risks.
- Policies set the WHY (security goals).
- Standards define the WHAT (mandatory rules).
- Procedures explain HOW (implementation steps).
- Guidelines provide best practices for security.
Following this hierarchy ensures security is clear, structured, and effective across an organization.